Image: HAVAL-192/4 Hash Algorithm Visualization
Published: January 7, 2026 at 10:45:48 PM UTC
Last updated: January 7, 2026 at 10:50:26 PM UTC
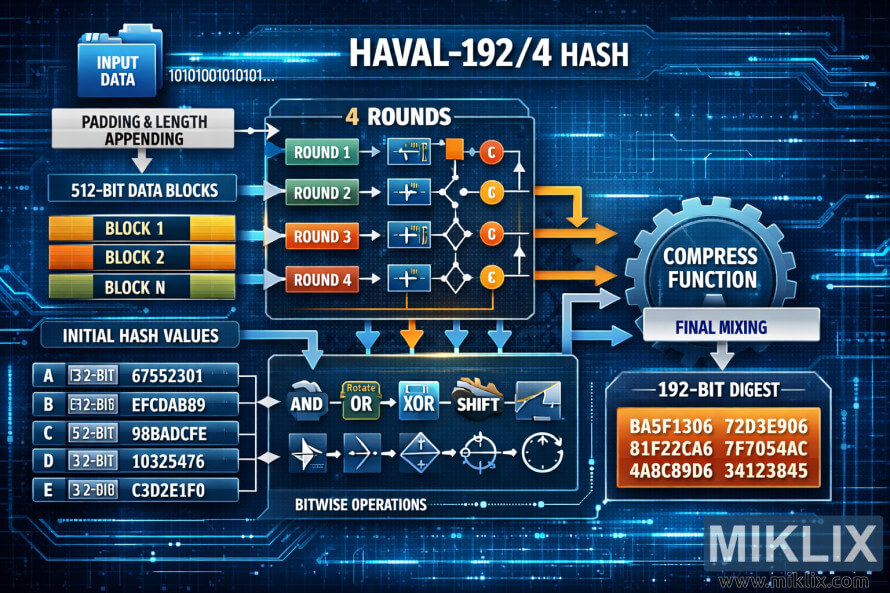
A detailed technical diagram showing the internal structure of the HAVAL-192/4 hash algorithm, including message padding, four transformation rounds, compression, and 192-bit output generation.
Available versions of this image
The image files available for download below are less compressed and higher resolution - and as a result of that, higher quality - than the images embedded in articles and pages on this website, which are more optimized for file size in order to reduce bandwidth consumption.
Regular size (1,536 x 1,024)
Large size (3,072 x 2,048)
Very large size (4,608 x 3,072)
Extra large size (6,144 x 4,096)
Comically large size (1,048,576 x 699,051)
- Still uploading... ;-)
Image description
This high-resolution landscape infographic provides a detailed visualization of the HAVAL-192/4 hash algorithm, a cryptographic function that produces a 192-bit hash output using four passes of compression and bitwise operations. The diagram presents a clear and systematic overview of the algorithm's internal workflow through color-coded components, directional arrows, and labeled processing blocks.
On the left side of the image, a blue folder labeled 'Input Data' represents the message to be hashed, accompanied by a binary stream (1010101010...) symbolizing raw input bits. Below this, a white rectangular box titled 'Padding & Length Appending' indicates the step where the message is extended and aligned to 512-bit blocks, ensuring proper formatting for processing.
Following this stage, three color-coded orange and green blocks labeled 'Block 1', 'Block 2', and 'Block N' represent the sequential 512-bit message chunks that enter the core of the algorithm. Each block is fed into the central processing section titled '4 Rounds', which is the most visually prominent element of the diagram. The four rounds are stacked vertically in a blue-bordered box, labeled 'Round 1', 'Round 2', 'Round 3', and 'Round 4', each associated with distinct colors—green for early stages and red for later ones. Each round includes icons representing mathematical and logical transformations such as bitwise rotations, shifts, XOR, AND, and OR operations, visualized as small mechanical and symbolic icons.
Arrows emanating from each round converge toward a large gear labeled 'Compress Function', visually representing the central mixing and compression phase of the HAVAL algorithm. Inside this section, additional arrows labeled 'Final Mixing' indicate the combination of intermediate states to form the final hash output.
In the lower left portion, a section labeled 'Initial Hash Values' lists five 32-bit constants used to initialize the hashing process. Each line (A through E) includes both the bit length and hexadecimal constants such as 67552301, EFCDAB89, 98BADCFE, 10325476, and C3D2E1F0, presented in metallic blue rectangles that visually suggest data registers. Directly below, another boxed area titled 'Bitwise Operations' displays a sequence of icons—AND, OR, XOR, SHIFT, ROTATE—connected by arrows to emphasize iterative and nonlinear transformations across multiple rounds.
Finally, at the bottom right corner of the diagram, a red and orange gradient box titled '192-Bit Digest' showcases the resulting six 32-bit words of the final hash output, displayed as hexadecimal values: BA5F1306, 72D3E906, 81F22CA6, 7F7054AC, 4A8C89D6, and 34123845.
The overall design features a blue, circuit-like background with faint electronic traces and grid patterns, evoking a high-tech digital environment. The typography is bold and modern, consistent with technical documentation and cybersecurity infographics. The visual flow, color contrast, and mechanical elements together create a clear yet complex representation of the HAVAL-192/4 hashing process, illustrating how input data is progressively transformed into a fixed-length cryptographic digest through structured, multi-stage computation.
The image is related to: HAVAL-192/4 Hash Code Calculator
