Image: High-Level Visualization of the SHA3-256 Hash Algorithm
Published: January 10, 2026 at 12:03:56 AM UTC
Last updated: January 10, 2026 at 12:04:10 AM UTC
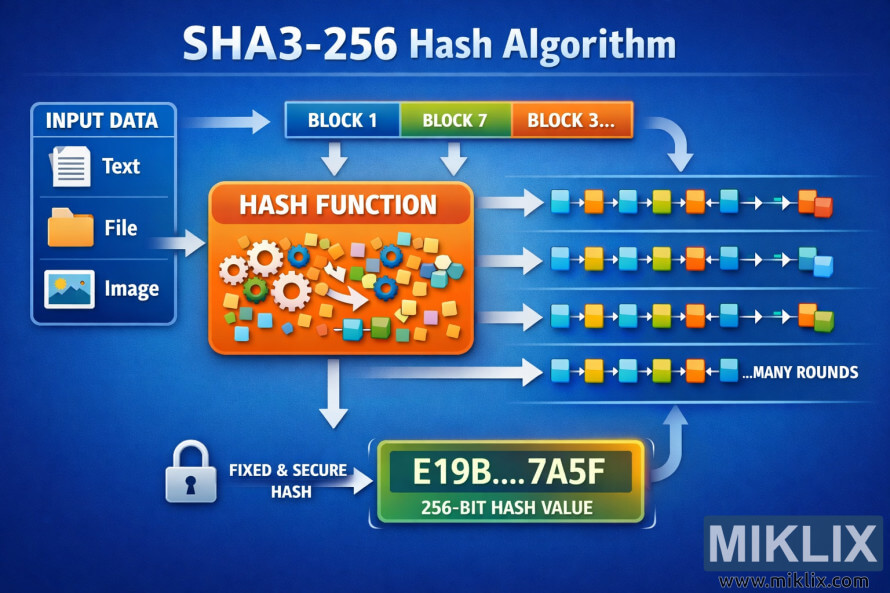
A clear, easy-to-understand infographic visualizing the SHA3-256 hash algorithm, showing how input data is transformed into a fixed-length digest.
Available versions of this image
The image files available for download below are less compressed and higher resolution - and as a result of that, higher quality - than the images embedded in articles and pages on this website, which are more optimized for file size in order to reduce bandwidth consumption.
Regular size (1,536 x 1,024)
Large size (3,072 x 2,048)
Very large size (4,608 x 3,072)
Extra large size (6,144 x 4,096)
Comically large size (1,048,576 x 699,051)
- Still uploading... ;-)
Image description
The image is a wide, landscape-oriented infographic that explains the overall idea of the SHA3-256 hashing process without diving into low-level implementation details. It is designed to be readable by non-experts while still conveying the structure of the algorithm.
On the far left, a panel labeled "Input Data" shows a stack of generic files, messages, and symbols flowing into a single stream. This visually represents that SHA3-256 can take any size or type of input. The elements gradually converge into a single arrow, emphasizing that all kinds of digital data are treated uniformly by the hash function.
The arrow leads to a central section titled "Preprocessing & Absorbing." Here, the data stream enters a large, softly rounded container. Inside this container are simple block shapes being drawn inward, illustrating the idea that the algorithm processes the input in chunks. The container is deliberately abstract, avoiding any concrete numbers, but it clearly communicates the idea of repeatedly feeding data into an internal state.
The middle of the image is the core visual focus: a large circular or square "State" area with subtle grid lines. Surrounding it are several looping arrows labeled with general terms such as "Mix," "Permute," and "Repeat." These arrows cycle around the state to show that SHA3-256 performs multiple rounds of internal transformation. The arrows are smooth and continuous, conveying the concept of diffusion and non-reversibility rather than exact operations. No specific constants or steps are named, preventing inaccuracies while still capturing the algorithm’s iterative nature.
To the right of the state, another arrow leads into a section titled "Squeezing Output." This panel shows the internal state releasing a stream of small blocks that merge into a single, compact bar. The visual metaphor suggests that after processing, the algorithm extracts a fixed amount of data from the state.
On the far right, the final panel is labeled "256-bit Hash." It shows a short, uniform string of hexadecimal-style characters inside a clean frame, representing the final digest. Next to it, small icons such as a shield and checkmark hint at properties like integrity and security, without listing technical guarantees.
The overall color palette is calm and modern, with blues and purples for the internal process and a contrasting accent color for the final hash. The background is light and uncluttered, and each section is clearly separated with gentle dividers and headings. The entire composition reads left to right like a story: any input goes in, it is absorbed and mixed repeatedly, and a short fixed-length hash comes out. The image communicates the purpose and flow of SHA3-256 at a conceptual level while staying neutral, accurate, and easy to understand.
The image is related to: SHA3-256 Hash Code Calculator
